Tutorial
Physical Layer
Data Link layer
Network Layer
Routing Algorithm
Transport Layer
Application Layer
Network Security
Misc
- Router
- OSI vs TCP/IP
- TCP vs UDP
- Transmission Control Protocol
- TCP port
- IPv4 vs IPv6
- ARP Packet Format
- ARP Table
- Working of ARP
- FTP Client
- FTP Commands
- FTP Server
- I2C Protocol
- Sliding Window Protocol
- SPI Protocol
- IP
- ARP Commands
- ARP
- Address Resolution Protocol
- ARP and its types
- TCP Retransmission
- CAN protocol
- HTTP Status Codes
- HTTP vs HTTPS
- RIP Protocol
- UDP Protocol
- ICMP Protocol
- MQTT protocol
- OSPF Protocol
- Stop and Wait Protocol
- IMAP Protocol
- POP Protocol
- CIFS
- DAS
- DIMM
- iSCSI
- NAS (Network Attached Storage)
- NFS
- NVMe
- SAN
- Border Gateway Protocol
- Go-Back-N ARQ
- RJ Cable
- Difference between Connection-Oriented and Connectionless Service
- CDMA vs. GSM
- What is MAC Address
- Modem vs. Router
- Switch Vs. Router
- USB 2.0 vs 3.0
- Difference between CSMA CA and CSMA CD
- Multiple access protocol- ALOHA, CSMA, CSMA/CA and CSMA/CD
- URI vs URL
- IMAP vs. POP3
- SSH Meaning| SSH Protocol
- UTP vs STP
- Status Code 400
- MIME Protocol
- IP address
- proxy server
- How to set up and use a proxy server
- network security
- WWW is based on which model
- Proxy Server List
- Fundamentals of Computer Networking
- IP Address Format and Table
- Bus topology and Ring topology
- Bus topology and Star topology
- Circuit Switching and Packet switching?
- Difference between star and ring topology
- Difference between Router and Bridge
- TCP Connection Termination
- Image Steganography
- Network Neutrality
- Onion Routing
- Adaptive security appliance (ASA) features
- Relabel-to-front Algorithm
- Types of Server Virtualization in Computer Network
- Access Lists (ACL)
- What is a proxy server and how does it work
- Digital Subscriber Line (DSL)
- Operating system based Virtualization
- Context based Access Control (CBAC)
- Cristian's Algorithm
- Service Set Identifier (SSID)
- Voice over Internet Protocol (VoIP)
- Challenge Response Authentication Mechanism (CRAM)
- Extended Access List
- Li-fi vs. Wi-fi
- Reflexive Access List
- Synchronous Optical Network (SONET)
- Wifi protected access (WPA)
- Wifi Protected Setup (WPS)
- Standard Access List
- Time Access List
- What is 3D Internet
- 4G Mobile Communication Technology
- Types of Wireless Transmission Media
- Best Computer Networking Courses
- Data Representation
- Network Criteria
- Classful vs Classless addressing
- Difference between BOOTP and RARP in Computer Networking
- What is AGP (Accelerated Graphics Port)
- Advantages and Disadvantages of Satellite Communication
- External IP Address
- Asynchronous Transfer Mode (ATM)
- Types of Authentication Protocols
- What is a CISCO Packet Tracer
- BOOTP work
- Subnetting in Computer Networks
- Mesh Topology Advantages and Disadvantages
- Ring Topology Advantages and Disadvantages
- Star Topology Advantages and Disadvantages
- Tree Topology Advantages and Disadvantages
- Zigbee Technology-The smart home protocol
- Network Layer in OSI Model
- Physical Layer in OSI Model
- Data Link Layer in OSI Model
- Internet explorer shortcut keys
- Network Layer Security | SSL Protocols
- Presentation Layer in OSI Model
- Session Layer in OSI Model
- SUBNET MASK
- Transport Layer Security | Secure Socket Layer (SSL) and SSL Architecture
- Functions, Advantages and Disadvantages of Network Layer
- Protocols in Noiseless and Noisy Channel
- Advantages and Disadvantages of Mesh Topology
- Cloud Networking - Managing and Optimizing Cloud-Based Networks
- Collision Domain and Broadcast Domain
- Count to Infinity Problem in Distance Vector Routing
- Difference Between Go-Back-N and Selective Repeat Protocol
- Difference between Stop and Wait, GoBackN, and Selective Repeat
- Network Function Virtualization (NFV): transforming Network Architecture with Virtualized Functions
- Network-Layer Security | IPSec Modes
- Next - Prev Network-Layer Security | IPSec Protocols and Services
- Ping vs Traceroute
- Software Defined Networking (SDN): Benefits and Challenges of Network Virtualization
- Software Defined Networking (SDN) vs. Network Function Virtualization (NFV)
- Virtual Circuits vs Datagram Networks
- BlueSmack Attack in Wireless Networks
- Bluesnarfing Attack in Wireless Networks
- Direct Sequence Spread Spectrum
- Warchalking in Wireless Networks
- WEP (Wired Equivalent Privacy)
- Wireless security encryption
- Wireless Security in an Enterprise
- Quantum Networking
- Network Automation
- Difference between MSS and MTU
- What is MTU
- Mesh Networks: A decentralized and Self-Organizing Approach to Networking
- What is Autonomous System
- What is MSS
- Cyber security & Software security
- Information security & Network security.
- Security Engineer & Security Architect
- Protection Methods for Network Security
- Trusted Systems in Network Security
- What are Authentication Tokens in Network security
- Cookies in Network Security
- Intruders in Network Security
- Network Security Toolkit (NST) in virtual box
- Pivoting-Moving Inside a Network
- Security Environment in Computer Networks
- Voice Biometric technique in Network Security
- Advantages and Disadvantages of Conventional Testing
- Difference between Kerberos and LDAP
- Cyber security and Information Security
- GraphQL Attacks and Security
- Application Layer in OSI Model
- Applications of Remote Sensing
- Seven Layers of IT Security
- What is Ad Hoc TCP
- What is Server Name Indication(SNI)
What is Server Name Indication(SNI)
This article will provide a detailed explanation of the topic called Server Name Indication(SNI). Before moving on to the main topic first, let us understand what is the server name.
What is Server Name?
A server name is just a computer's name. Users are not shown this name in the case of web servers unless the server only hosts one domain and its name is the same as the domain name. The clients provide that hostname by which they can connect at the before handshaking using the Server Name Indication feature of the Transport Layer Security computer networking protocol.
What is Server Name Indication(SNI)?
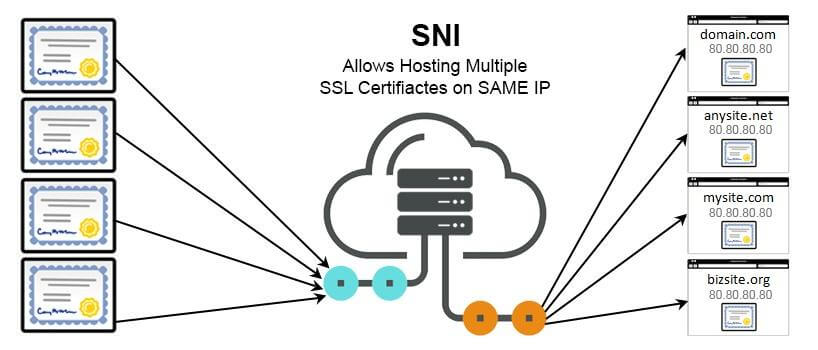
Server Name Indication (SNI) is an extension of the TLS protocol. At the beginning of the TLS handshake, a client or browser is permitted to specify the hostname through which he/she can connect. With the same IP address and port, the server may thus show a number of certificates. Before SNI, only one SSL/TLS certificate could be issued per IP address, making it impossible to run several secure websites on the same server.
Why Use Server Name Identification?
IP addresses are very deficient sources i.e., they are available in very less number. So, SNI helps in protecting these IP addresses.
Some other important reasons of using SNI are mentioned below:
- website that requires SSL/TLS encryption need not require to set up a separate IP address by using SNI.
- SNI makes the connection simpler for website administrators and owners to maintain SSL/TLS certificates.
- SNI enables servers to host several TLS certificates for numerous sites under a single IP address.
- SNI offers the benefit of hiding the certificate from scanning, which helps to boost security.
Working of SNI
- The "ClientHello" message is sent by the client to the server as part of a TLS handshake.
- The hostname of the server that the client wants to connect is included in the "ClientHello" message.
- The requested hostname's SSL/TLS certificate is included in the "ServerHello" message which the server sends back as a response.
- The server will respond with an error message and cut off the connection if it doesn't support SNI or doesn't have a certificate for the requested hostname.
- The client and server will finish the TLS handshake and start the encrypted connection if the server has a valid SSL/TLS certificate for the specified hostname.

Modern web browsers and servers, like Apache and Nginx, support SNI to a large extent. SNI may not be supported by older servers and browsers, which might cause compatibility problems.
Features of Server Name Identification
Following are the some features or characteristics of Server Name Identification:
- Cost Savings: IP addresses are very expensive to obtain and use. SNI helps in reducing the need for additional IP addresses for hosting multiple websites. So, lots of money can be saved as the there is no necessity for additional IP addresses.
- Compatibility: SNI is a widely used technique for hosting several secure websites on a single server because the majority of modern web browsers and servers support it.
- Multiple certificates: In order to host many domain names on the same IP address, SNI permits the installation of numerous SSL/TLS certificates on a single server.
- Improved Performance: SNI lets the servers to handle more requests and make better use of their resources, which can speed up websites.
- Enhanced Security: In order to improve security and fend against man-in-the-middle attacks, SNI makes sure that the appropriate SSL/TLS certificate is being utilised for each domain name.
- Flexibility: SNI offers flexibility by hosting multiple domains i.e., SNI allows a single server to host different websites where each having its OWN SSL/TLS certificate.
Benefits of Server Name Identification
Following are the four benefits of Server Name Identification:
- Better resource utilization: The main benefit of using SNI is that it allows several SSL certificates to be hosted on a single IP address. This will help in eliminating waste and maximizing resource efficiency.
- Simplified management: The Server Name Identification minimizes the complexity of SSL certificate administration which allows many SSL certificates to be hosted on a single IP address.
- Support for virtual hosting: The cost of hosting SSL certificates is further decreased because of SNI's compatibility with virtual hosting.
Virtual hosting is the process of running several websites on a single server, allowing different domains to share server resources like CPU, memory, and storage. Virtual hosting also allows website owners to host numerous websites on a single physical server which eliminates the need for additional servers and helps in reducing the cost. - Improved Server Efficiency: Server Name Identification increases the server efficiency by reducing the number of IP addresses required for SSL certificates.
Limitations of Server Name Identification
With the benefits of SNI, it also has some limitations which are discussed below:
- Limited to HTTPS: Server Name Identification is only used for HTTPS connections. So, it has no advantages over other protocols like FTP or SMTP.
- Lack of Encrypted SNI Support: The information of Server Name Identification is transmitted in plain text during the TLS handshake, which makes it possible for third parties to view the domain name of the website being accessed. To overcome this limitation, we can use the encrypted SNI, but it is not supported by many systems.
- Complexity: Server Name Identification increases the complexity of the SSL/TLS negotiation process, which might lead to more setup mistakes or SSL certificate management mistakes.
- Performance: SNI may add additional round trips between the client and server, which may increase latency and reduce the performance.
- Single Certificate Per IP Address: The main disadvantage of SNI is that it uses single certificate for one IP address. This can create a problem if many websites are hosted on the same IP address under different certificates.


