Tutorial
Physical Layer
Data Link layer
Network Layer
Routing Algorithm
Transport Layer
Application Layer
Network Security
Misc
- Router
- OSI vs TCP/IP
- TCP vs UDP
- Transmission Control Protocol
- TCP port
- IPv4 vs IPv6
- ARP Packet Format
- ARP Table
- Working of ARP
- FTP Client
- FTP Commands
- FTP Server
- I2C Protocol
- Sliding Window Protocol
- SPI Protocol
- IP
- ARP Commands
- ARP
- Address Resolution Protocol
- ARP and its types
- TCP Retransmission
- CAN protocol
- HTTP Status Codes
- HTTP vs HTTPS
- RIP Protocol
- UDP Protocol
- ICMP Protocol
- MQTT protocol
- OSPF Protocol
- Stop and Wait Protocol
- IMAP Protocol
- POP Protocol
- CIFS
- DAS
- DIMM
- iSCSI
- NAS (Network Attached Storage)
- NFS
- NVMe
- SAN
- Border Gateway Protocol
- Go-Back-N ARQ
- RJ Cable
- Difference between Connection-Oriented and Connectionless Service
- CDMA vs. GSM
- What is MAC Address
- Modem vs. Router
- Switch Vs. Router
- USB 2.0 vs 3.0
- Difference between CSMA CA and CSMA CD
- Multiple access protocol- ALOHA, CSMA, CSMA/CA and CSMA/CD
- URI vs URL
- IMAP vs. POP3
- SSH Meaning| SSH Protocol
- UTP vs STP
- Status Code 400
- MIME Protocol
- IP address
- proxy server
- How to set up and use a proxy server
- network security
- WWW is based on which model
- Proxy Server List
- Fundamentals of Computer Networking
- IP Address Format and Table
- Bus topology and Ring topology
- Bus topology and Star topology
- Circuit Switching and Packet switching?
- Difference between star and ring topology
- Difference between Router and Bridge
- TCP Connection Termination
- Image Steganography
- Network Neutrality
- Onion Routing
- Adaptive security appliance (ASA) features
- Relabel-to-front Algorithm
- Types of Server Virtualization in Computer Network
- Access Lists (ACL)
- What is a proxy server and how does it work
- Digital Subscriber Line (DSL)
- Operating system based Virtualization
- Context based Access Control (CBAC)
- Cristian's Algorithm
- Service Set Identifier (SSID)
- Voice over Internet Protocol (VoIP)
- Challenge Response Authentication Mechanism (CRAM)
- Extended Access List
- Li-fi vs. Wi-fi
- Reflexive Access List
- Synchronous Optical Network (SONET)
- Wifi protected access (WPA)
- Wifi Protected Setup (WPS)
- Standard Access List
- Time Access List
- What is 3D Internet
- 4G Mobile Communication Technology
- Types of Wireless Transmission Media
- Best Computer Networking Courses
- Data Representation
- Network Criteria
- Classful vs Classless addressing
- Difference between BOOTP and RARP in Computer Networking
- What is AGP (Accelerated Graphics Port)
- Advantages and Disadvantages of Satellite Communication
- External IP Address
- Asynchronous Transfer Mode (ATM)
- Types of Authentication Protocols
- What is a CISCO Packet Tracer
- BOOTP work
- Subnetting in Computer Networks
- Mesh Topology Advantages and Disadvantages
- Ring Topology Advantages and Disadvantages
- Star Topology Advantages and Disadvantages
- Tree Topology Advantages and Disadvantages
- Zigbee Technology-The smart home protocol
- Network Layer in OSI Model
- Physical Layer in OSI Model
- Data Link Layer in OSI Model
- Internet explorer shortcut keys
- Network Layer Security | SSL Protocols
- Presentation Layer in OSI Model
- Session Layer in OSI Model
- SUBNET MASK
- Transport Layer Security | Secure Socket Layer (SSL) and SSL Architecture
- Functions, Advantages and Disadvantages of Network Layer
- Protocols in Noiseless and Noisy Channel
- Advantages and Disadvantages of Mesh Topology
- Cloud Networking - Managing and Optimizing Cloud-Based Networks
- Collision Domain and Broadcast Domain
- Count to Infinity Problem in Distance Vector Routing
- Difference Between Go-Back-N and Selective Repeat Protocol
- Difference between Stop and Wait, GoBackN, and Selective Repeat
- Network Function Virtualization (NFV): transforming Network Architecture with Virtualized Functions
- Network-Layer Security | IPSec Modes
- Next - Prev Network-Layer Security | IPSec Protocols and Services
- Ping vs Traceroute
- Software Defined Networking (SDN): Benefits and Challenges of Network Virtualization
- Software Defined Networking (SDN) vs. Network Function Virtualization (NFV)
- Virtual Circuits vs Datagram Networks
- BlueSmack Attack in Wireless Networks
- Bluesnarfing Attack in Wireless Networks
- Direct Sequence Spread Spectrum
- Warchalking in Wireless Networks
- WEP (Wired Equivalent Privacy)
- Wireless security encryption
- Wireless Security in an Enterprise
- Quantum Networking
- Network Automation
- Difference between MSS and MTU
- What is MTU
- Mesh Networks: A decentralized and Self-Organizing Approach to Networking
- What is Autonomous System
- What is MSS
- Cyber security & Software security
- Information security & Network security.
- Security Engineer & Security Architect
- Protection Methods for Network Security
- Trusted Systems in Network Security
- What are Authentication Tokens in Network security
- Cookies in Network Security
- Intruders in Network Security
- Network Security Toolkit (NST) in virtual box
- Pivoting-Moving Inside a Network
- Security Environment in Computer Networks
- Voice Biometric technique in Network Security
- Advantages and Disadvantages of Conventional Testing
- Difference between Kerberos and LDAP
- Cyber security and Information Security
- GraphQL Attacks and Security
- Application Layer in OSI Model
- Applications of Remote Sensing
- Seven Layers of IT Security
- What is Ad Hoc TCP
- What is Server Name Indication(SNI)
HTTP vs HTTPS
An HTTP stands for Hypertext Transfer Protocol. The HTTP protocol provides communication between different communication systems. When the user makes an HTTP request on the browser, then the webserver sends the requested data to the user in the form of web pages. In short, we can say that the HTTP protocol allows us to transfer the data from the server to the client.
An HTTP is an application layer protocol that comes above the TCP layer. It has provided some standard rules to the web browsers and servers, which they can use to communicate with each other.
An HTTP is a stateless protocol as each transaction is executed separately without having any knowledge of the previous transactions, which means that once the transaction is completed between the web browser and the server, the connection gets lost.
What is HTTPS?
The full form of HTTPS is Hypertext Transfer Protocol Secure. The HTTP protocol does not provide the security of the data, while HTTP ensures the security of the data. Therefore, we can say that HTTPS is a secure version of the HTTP protocol. This protocol allows transferring the data in an encrypted form. The use of HTTPS protocol is mainly required where we need to enter the bank account details. The HTTPS protocol is mainly used where we require to enter the login credentials. In modern browsers such as chrome, both the protocols, i.e., HTTP and HTTPS, are marked differently. To provide encryption, HTTPS uses an encryption protocol known as Transport Layer Security, and officially, it is referred to as a Secure Sockets Layer (SSL). This protocol uses a mechanism known as asymmetric public key infrastructure, and it uses two different keys which are given below:
- Private key: This key is available on the web server, which is managed by the owner of a website.
- It decrypts the information which is encrypted by the public key.
- Public key: This key is available to everyone. It converts the data into an encrypted form.
Main difference between the HTTP and HTTPS
The major difference between the HTTP and HTTPS is the SSL certificate. The HTTPS protocol is an extended version of the HTTP protocol with an additional feature of security.
This additional feature of security is very important for those websites which transmit sensitive data such as credit card information.
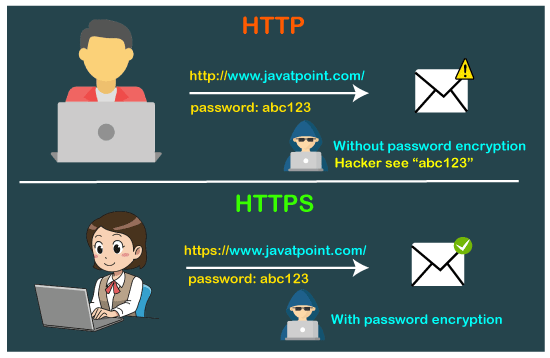
The HTTPS protocol is secured due to the SSL protocol. The SSL protocol encrypts the data which the client transmits to the server. If someone tries to steal the information which is being communicated between the client and the server, then he/she would not be able to understand due to the encryption. This is the main difference between the HTTP and HTTPS that the HTTP does not contain SSL, whereas the HTTPS contains SSL that provides secure communication between the client and the server.
Which is better, HTTP or HTTPS?
Till now, we read that the HTTPS is better than HTTP because it provides security. Sometimes our website does not contain an e-commerce page that requires sensitive data; in that case, we can switch to the HTTP protocol. Despite the security, HTTPS also provides SEO. So, we do need to put more effort into boosting our SEO.
HTTP vs HTTPS performance
The speed of HTTP is faster than the HTTPS as the HTTPS contains SSL protocol, while HTTPS does not contain an SSL protocol. This additional feature of SSL in HTTPS makes the page loading slower.
Differences between HTTP and HTTPS
The following are the differences between the HTTP and HTTPS:
- Protocol
The HTTP protocol stands for Hypertext Transfer Protocol, whereas the HTTPS stands for Hypertext Transfer Protocol Secure.
- Security
The HTTP protocol is not secure protocol as it does not contain SSL (Secure Sockets Layer), which means that the data can be stolen when the data is transmitted from the client to the server. Whereas, the HTTPS protocol contains the SSL certificate that converts the data into an encrypted form, so no data can be stolen in this case as outsiders do not understand the encrypted text.
- Port numbers
The HTTP transmits the data over port number 80, whereas the HTTPS transmits the data over 443 port number. Under the documentation issued by Tim Berners-Lee, he stated that "if the port number is not specified, then it will be considered as HTTP".
When RFC 1340 was announced, then the IETF (Internet Engineering Task Force) provided port number 80 to the HTTP. When the new RFC was released in the year 1994, the HTTPS is assigned with a port number 443.
- Layers
The HTTP protocol works on the application layer while the HTTPS protocol works on the transport layer. As we know that the responsibility of the transport layer is to move the data from the client to the server, and data security is a major concern. HTTPS operates in the transport layer, so it is wrapped with a security layer.
- SSL Certificates
When we want our websites to have an HTTPS protocol, then we need to install the signed SSL certificate. The SSL certificates can be available for both free and paid service. The service can be chosen based on business needs.
The HTTP does not contain any SSL certificates, so it does not decrypt the data, and the data is sent in the form of plain text.
- SEO Advantages
The SEO advantages are provided to those websites that use HTTPS as GOOGLE gives the preferences to those websites that use HTTPS rather than the websites that use HTTP.
- Online Transactions
If we are running an online business, then it becomes necessary to have HTTPS. If we do not use the HTTPS in an online business, then the customers would not purchase as they are scared that their data can be stolen by the outsiders.
Let's understand the differences in a tabular form.
| HTTP | HTTPS |
|---|---|
| The full form of HTTP is the Hypertext Transfer Protocol. | The full form of HTTPS is Hypertext Transfer Protocol Secure. |
| It is written in the address bar as http://. | It is written in the address bar as https://. |
| The HTTP transmits the data over port number 80. | The HTTPS transmits the data over port number 443. |
| It is unsecured as the plain text is sent, which can be accessible by the hackers. | It is secure as it sends the encrypted data which hackers cannot understand. |
| It is mainly used for those websites that provide information like blog writing. | It is a secure protocol, so it is used for those websites that require to transmit the bank account details or credit card numbers. |
| It is an application layer protocol. | It is a transport layer protocol. |
| It does not use SSL. | It uses SSL that provides the encryption of the data. |
| Google does not give the preference to the HTTP websites. | Google gives preferences to the HTTPS as HTTPS websites are secure websites. |
| The page loading speed is fast. | The page loading speed is slow as compared to HTTP because of the additional feature that it supports, i.e., security. |


