Tutorial
Physical Layer
Data Link layer
Network Layer
Routing Algorithm
Transport Layer
Application Layer
Network Security
Misc
- Router
- OSI vs TCP/IP
- TCP vs UDP
- Transmission Control Protocol
- TCP port
- IPv4 vs IPv6
- ARP Packet Format
- ARP Table
- Working of ARP
- FTP Client
- FTP Commands
- FTP Server
- I2C Protocol
- Sliding Window Protocol
- SPI Protocol
- IP
- ARP Commands
- ARP
- Address Resolution Protocol
- ARP and its types
- TCP Retransmission
- CAN protocol
- HTTP Status Codes
- HTTP vs HTTPS
- RIP Protocol
- UDP Protocol
- ICMP Protocol
- MQTT protocol
- OSPF Protocol
- Stop and Wait Protocol
- IMAP Protocol
- POP Protocol
- CIFS
- DAS
- DIMM
- iSCSI
- NAS (Network Attached Storage)
- NFS
- NVMe
- SAN
- Border Gateway Protocol
- Go-Back-N ARQ
- RJ Cable
- Difference between Connection-Oriented and Connectionless Service
- CDMA vs. GSM
- What is MAC Address
- Modem vs. Router
- Switch Vs. Router
- USB 2.0 vs 3.0
- Difference between CSMA CA and CSMA CD
- Multiple access protocol- ALOHA, CSMA, CSMA/CA and CSMA/CD
- URI vs URL
- IMAP vs. POP3
- SSH Meaning| SSH Protocol
- UTP vs STP
- Status Code 400
- MIME Protocol
- IP address
- proxy server
- How to set up and use a proxy server
- network security
- WWW is based on which model
- Proxy Server List
- Fundamentals of Computer Networking
- IP Address Format and Table
- Bus topology and Ring topology
- Bus topology and Star topology
- Circuit Switching and Packet switching?
- Difference between star and ring topology
- Difference between Router and Bridge
- TCP Connection Termination
- Image Steganography
- Network Neutrality
- Onion Routing
- Adaptive security appliance (ASA) features
- Relabel-to-front Algorithm
- Types of Server Virtualization in Computer Network
- Access Lists (ACL)
- What is a proxy server and how does it work
- Digital Subscriber Line (DSL)
- Operating system based Virtualization
- Context based Access Control (CBAC)
- Cristian's Algorithm
- Service Set Identifier (SSID)
- Voice over Internet Protocol (VoIP)
- Challenge Response Authentication Mechanism (CRAM)
- Extended Access List
- Li-fi vs. Wi-fi
- Reflexive Access List
- Synchronous Optical Network (SONET)
- Wifi protected access (WPA)
- Wifi Protected Setup (WPS)
- Standard Access List
- Time Access List
- What is 3D Internet
- 4G Mobile Communication Technology
- Types of Wireless Transmission Media
- Best Computer Networking Courses
- Data Representation
- Network Criteria
- Classful vs Classless addressing
- Difference between BOOTP and RARP in Computer Networking
- What is AGP (Accelerated Graphics Port)
- Advantages and Disadvantages of Satellite Communication
- External IP Address
- Asynchronous Transfer Mode (ATM)
- Types of Authentication Protocols
- What is a CISCO Packet Tracer
- BOOTP work
- Subnetting in Computer Networks
- Mesh Topology Advantages and Disadvantages
- Ring Topology Advantages and Disadvantages
- Star Topology Advantages and Disadvantages
- Tree Topology Advantages and Disadvantages
- Zigbee Technology-The smart home protocol
- Network Layer in OSI Model
- Physical Layer in OSI Model
- Data Link Layer in OSI Model
- Internet explorer shortcut keys
- Network Layer Security | SSL Protocols
- Presentation Layer in OSI Model
- Session Layer in OSI Model
- SUBNET MASK
- Transport Layer Security | Secure Socket Layer (SSL) and SSL Architecture
- Functions, Advantages and Disadvantages of Network Layer
- Protocols in Noiseless and Noisy Channel
- Advantages and Disadvantages of Mesh Topology
- Cloud Networking - Managing and Optimizing Cloud-Based Networks
- Collision Domain and Broadcast Domain
- Count to Infinity Problem in Distance Vector Routing
- Difference Between Go-Back-N and Selective Repeat Protocol
- Difference between Stop and Wait, GoBackN, and Selective Repeat
- Network Function Virtualization (NFV): transforming Network Architecture with Virtualized Functions
- Network-Layer Security | IPSec Modes
- Next - Prev Network-Layer Security | IPSec Protocols and Services
- Ping vs Traceroute
- Software Defined Networking (SDN): Benefits and Challenges of Network Virtualization
- Software Defined Networking (SDN) vs. Network Function Virtualization (NFV)
- Virtual Circuits vs Datagram Networks
- BlueSmack Attack in Wireless Networks
- Bluesnarfing Attack in Wireless Networks
- Direct Sequence Spread Spectrum
- Warchalking in Wireless Networks
- WEP (Wired Equivalent Privacy)
- Wireless security encryption
- Wireless Security in an Enterprise
- Quantum Networking
- Network Automation
- Difference between MSS and MTU
- What is MTU
- Mesh Networks: A decentralized and Self-Organizing Approach to Networking
- What is Autonomous System
- What is MSS
- Cyber security & Software security
- Information security & Network security.
- Security Engineer & Security Architect
- Protection Methods for Network Security
- Trusted Systems in Network Security
- What are Authentication Tokens in Network security
- Cookies in Network Security
- Intruders in Network Security
- Network Security Toolkit (NST) in virtual box
- Pivoting-Moving Inside a Network
- Security Environment in Computer Networks
- Voice Biometric technique in Network Security
- Advantages and Disadvantages of Conventional Testing
- Difference between Kerberos and LDAP
- Cyber security and Information Security
- GraphQL Attacks and Security
- Application Layer in OSI Model
- Applications of Remote Sensing
- Seven Layers of IT Security
- What is Ad Hoc TCP
- What is Server Name Indication(SNI)
Star Topology Advantages and Disadvantages
To understand the advantages and disadvantages, first we have to know about the what is Star Topology? So, let's begin with introduction.
What is Star Topology?
The star topology is a standard and popular network setup. it is also known as a star network in terms. This topology is a network topology in which each piece of the network each attached to a central node. This central node is called a switch or a hub. In this network configuration, every node connects to a central network device like a switch, hub, or computer.
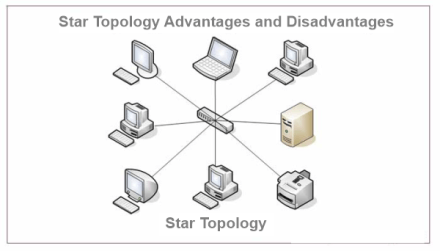
In this configuration, the central network device behaves like a server, and the peripheral devices behave like clients. We can say in this configuration; a central hub acts like a channel to transmit messages. An RJ-45 or a coaxial network cable is used in the setup of a star topology network, which depends on the type of network card installed in each computer. The star network is a very popular computer network topology in the industry.
The attachment for these network pieces to the central component is presented visually to show like a star. That's why it is also known as a star network.
The star topologies can be either passive or active networks depending on the following points:
- Whether the data transit in the network is controlled activity.
- Whether the electrical power sources are required by the network.
- Whether the central node performs data regeneration or amplification or any type of such kind of process.
Star topology can also be implemented with cable structures, Ethernet, wireless routers are other components. In many cases, the server is the central hub for the systems, and the additional nodes are the clients.
Advantages of Star Topology:
There are many advantages of using star topology which are described below:
1. User friendly:
Without affecting the rest of the network, the new nodes can be added easily to the star topology. In that manner, we can easily remove the components in it. So it is convenient to add more computers to the network. It also becomes easier to replace a damaged unit to maintain our productivity levels.
2. Centralized network:
The network is monitored with the help of a centralized management system using the hub, central computer, or switch.
3. Very reliable:
When a device or a cable fails, then the other devices which are connected to it will Work. Hence the rest of the network is not affected by the failure of one node or link.
4. Highly efficient:
Within the star topology, when each device is connected to the central core with the help of cables, then the chances of collision of data are relatively lower. From that, it means the system's performance level is higher than expected compared to other network designs.
5. Easily manageable:
Within the star topology, fault detection is easily manageable. It is because the link is often easily identified. On the other hand, in the star topology, troubleshooting and detecting failure is very easy.
6. No point-to-point connection:
A start apology system is very useful for networks that are practical of any size. Within this network, the signal reflection is at zero risk. With the help of point-based communication connections and unicast communication, it creates a secure way to transmit data packets.
7. Safe to use:
When a NIC failure is a cut cable experienced in a star topology, it will only affect one node.
By disabling the central core, we can simultaneously take down all of the devices. Since the central device is not available easily for everyone, it is a secure and safe network for businesses of any size that can use it to support their needs.
8. Multiple stars can be created to extend the network's reach:
With the help of star topology, we can easily extend the length of the network right and progress on our from multiple stars in the middle with their central core as a server. Even if to support all the activities to be functional for this approach, there must be enough power in this network.
Disadvantages of Star Topology:
Like many advantages of a star topology, there are also many disadvantages. The disadvantages of star topology are given below;
1. High cost:
Within the star topology implementation of a router or switch, it's very costly, especially when using a router or a switch as the central network device.
2. Central device Dependency:
Within the star topology, when a hub malfunctions, then everything goes down because no devices can work without a hub. The main negative point in this whole network is when the central device goes down or fails, the whole system goes down.
3. High maintenance:
Within the star topology, regular maintenance and more resources are required by the hub because it is the central system of the star.
4. Prone to damage:
Within the star topology, more potential damage exposure is created by the cables are wires used in it.
It needs to go behind under floors, walls, and through other obstacles To reach the intended peripherals or workstations. Also, if the LAN needs installation work on the exterior building, it becomes susceptible to changing wildlife impacts or weather conditions.
5. Low data transfer rates in the wireless system:
To manage heavy loads when we require a network,
Then a wired star topology system works better instead of a wireless one. A wireless LAN (WLAN) mobs much slower, so the risk of a bottleneck rises.
6. Immobile network system:
Although wireless star topology systems are available today, We are the most dependent on wired connections.So that it means the fixed length of the cable restricts the movement of the individual employees. Dramatically over time, this type of issue can reduce the level of productivity because one gets bound to sit at a particular distance from the central hub of the network system.
Comparison between advantages and disadvantages of star topology:
| Advantages | Disadvantages |
|---|---|
| 1. Its speed is very high. | 1. Maintenance cost is very high. |
| 2. The network is highly scalable. | 2. Central device dependency |
| 3. It is the most efficient. | 3. It is very expensive. |
| 4. It has a centralized network management system. | 4. It requires additional equipment. |
| 5. It is very safe to use. | 5. The system is immobile. |
| 6. There are no point-to-point connections. | 6. Cables are wires used in this network got damaged very easily. |
| 7. It is very reliable. | 7. The data transfer rate is very low in wireless star topology systems. |
Summary:
The star topology system works well for Local Area Networks (LAN) when multiple connection points are necessary for a network. And as discussed earlier, the central hub might be expensive to install, but the data packet movement is typically faster because it is self-contained.


