Tutorial
Physical Layer
Data Link layer
Network Layer
Routing Algorithm
Transport Layer
Application Layer
Network Security
Misc
- Router
- OSI vs TCP/IP
- TCP vs UDP
- Transmission Control Protocol
- TCP port
- IPv4 vs IPv6
- ARP Packet Format
- ARP Table
- Working of ARP
- FTP Client
- FTP Commands
- FTP Server
- I2C Protocol
- Sliding Window Protocol
- SPI Protocol
- IP
- ARP Commands
- ARP
- Address Resolution Protocol
- ARP and its types
- TCP Retransmission
- CAN protocol
- HTTP Status Codes
- HTTP vs HTTPS
- RIP Protocol
- UDP Protocol
- ICMP Protocol
- MQTT protocol
- OSPF Protocol
- Stop and Wait Protocol
- IMAP Protocol
- POP Protocol
- CIFS
- DAS
- DIMM
- iSCSI
- NAS (Network Attached Storage)
- NFS
- NVMe
- SAN
- Border Gateway Protocol
- Go-Back-N ARQ
- RJ Cable
- Difference between Connection-Oriented and Connectionless Service
- CDMA vs. GSM
- What is MAC Address
- Modem vs. Router
- Switch Vs. Router
- USB 2.0 vs 3.0
- Difference between CSMA CA and CSMA CD
- Multiple access protocol- ALOHA, CSMA, CSMA/CA and CSMA/CD
- URI vs URL
- IMAP vs. POP3
- SSH Meaning| SSH Protocol
- UTP vs STP
- Status Code 400
- MIME Protocol
- IP address
- proxy server
- How to set up and use a proxy server
- network security
- WWW is based on which model
- Proxy Server List
- Fundamentals of Computer Networking
- IP Address Format and Table
- Bus topology and Ring topology
- Bus topology and Star topology
- Circuit Switching and Packet switching?
- Difference between star and ring topology
- Difference between Router and Bridge
- TCP Connection Termination
- Image Steganography
- Network Neutrality
- Onion Routing
- Adaptive security appliance (ASA) features
- Relabel-to-front Algorithm
- Types of Server Virtualization in Computer Network
- Access Lists (ACL)
- What is a proxy server and how does it work
- Digital Subscriber Line (DSL)
- Operating system based Virtualization
- Context based Access Control (CBAC)
- Cristian's Algorithm
- Service Set Identifier (SSID)
- Voice over Internet Protocol (VoIP)
- Challenge Response Authentication Mechanism (CRAM)
- Extended Access List
- Li-fi vs. Wi-fi
- Reflexive Access List
- Synchronous Optical Network (SONET)
- Wifi protected access (WPA)
- Wifi Protected Setup (WPS)
- Standard Access List
- Time Access List
- What is 3D Internet
- 4G Mobile Communication Technology
- Types of Wireless Transmission Media
- Best Computer Networking Courses
- Data Representation
- Network Criteria
- Classful vs Classless addressing
- Difference between BOOTP and RARP in Computer Networking
- What is AGP (Accelerated Graphics Port)
- Advantages and Disadvantages of Satellite Communication
- External IP Address
- Asynchronous Transfer Mode (ATM)
- Types of Authentication Protocols
- What is a CISCO Packet Tracer
- BOOTP work
- Subnetting in Computer Networks
- Mesh Topology Advantages and Disadvantages
- Ring Topology Advantages and Disadvantages
- Star Topology Advantages and Disadvantages
- Tree Topology Advantages and Disadvantages
- Zigbee Technology-The smart home protocol
- Network Layer in OSI Model
- Physical Layer in OSI Model
- Data Link Layer in OSI Model
- Internet explorer shortcut keys
- Network Layer Security | SSL Protocols
- Presentation Layer in OSI Model
- Session Layer in OSI Model
- SUBNET MASK
- Transport Layer Security | Secure Socket Layer (SSL) and SSL Architecture
- Functions, Advantages and Disadvantages of Network Layer
- Protocols in Noiseless and Noisy Channel
- Advantages and Disadvantages of Mesh Topology
- Cloud Networking - Managing and Optimizing Cloud-Based Networks
- Collision Domain and Broadcast Domain
- Count to Infinity Problem in Distance Vector Routing
- Difference Between Go-Back-N and Selective Repeat Protocol
- Difference between Stop and Wait, GoBackN, and Selective Repeat
- Network Function Virtualization (NFV): transforming Network Architecture with Virtualized Functions
- Network-Layer Security | IPSec Modes
- Next - Prev Network-Layer Security | IPSec Protocols and Services
- Ping vs Traceroute
- Software Defined Networking (SDN): Benefits and Challenges of Network Virtualization
- Software Defined Networking (SDN) vs. Network Function Virtualization (NFV)
- Virtual Circuits vs Datagram Networks
- BlueSmack Attack in Wireless Networks
- Bluesnarfing Attack in Wireless Networks
- Direct Sequence Spread Spectrum
- Warchalking in Wireless Networks
- WEP (Wired Equivalent Privacy)
- Wireless security encryption
- Wireless Security in an Enterprise
- Quantum Networking
- Network Automation
- Difference between MSS and MTU
- What is MTU
- Mesh Networks: A decentralized and Self-Organizing Approach to Networking
- What is Autonomous System
- What is MSS
- Cyber security & Software security
- Information security & Network security.
- Security Engineer & Security Architect
- Protection Methods for Network Security
- Trusted Systems in Network Security
- What are Authentication Tokens in Network security
- Cookies in Network Security
- Intruders in Network Security
- Network Security Toolkit (NST) in virtual box
- Pivoting-Moving Inside a Network
- Security Environment in Computer Networks
- Voice Biometric technique in Network Security
- Advantages and Disadvantages of Conventional Testing
- Difference between Kerberos and LDAP
- Cyber security and Information Security
- GraphQL Attacks and Security
- Application Layer in OSI Model
- Applications of Remote Sensing
- Seven Layers of IT Security
- What is Ad Hoc TCP
- What is Server Name Indication(SNI)
Types of Wireless Transmission Media
When we talk about a Headset or Earphones, there are wired regular earphones that we physically connect to our phones, and there are wireless Bluetooth headsets that we connect via Bluetooth. Transmission via Bluetooth is one of the simplest and most prominent examples of wireless transmission media.
Wireless data transmission is also called "Unguided Transmission" or "Unbounded Transmission" because of the absence of physical boundaries. When we turn on the Bluetooth on our phone and connect a headset, our phone and the device communicate with each other using ultra high-frequency Radio waves-one of the wireless transmission media.
This tutorial explains about three major wireless transmission media in details with examples around us.
1. Infrared Transmission
IR or Infrared radiation is a part of electromagnetic radiation. These rays have a wavelength greater than visible light, making them invisible to the human eye. We cannot see Infrared light but feel the rays in the form of heat. Frequency range: 300 GHz to 400 THz.
When we look at a fire, we can feel the heat from it and see it because it emits visible light and Infrared energy. The human body also emits heat but only in the form of Infrared light. Instruments such as night-vision goggles and Infrared cameras can capture Infrared light.
Sun is the biggest source of Infrared radiation. Hence, it causes a lot of interference in Infrared communication. One most important point about Infrared rays is that these rays cannot penetrate through walls. Hence, the applications of Infrared rays lie within a contained space.
So, how does the data transfer take place using this Infrared light?
Let us apply for Infrared data transfer and see how it is happening. The most used application is the "TV Remote control". When we press a button on the remote, how is it changing the channel on the TV?

An Infrared Light emitting diode is embedded into the TV remote and an IR detector is inserted into the TV. This detector converts the Infrared light signal from the remote and converts it into an electrical signal. Hence, the remote acts as a transmitter and the TV as a receiver.

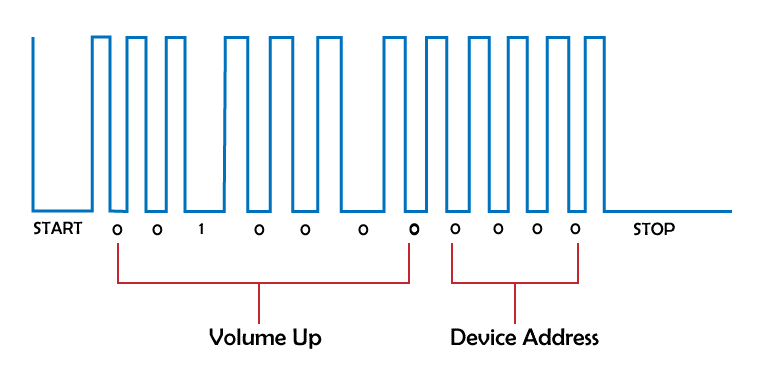
All the buttons on a TV remote are connected to a microprocessor which generates a unique binary code for each button pressed. All these codes will be of the same length. The LED flashes on and off according to the generated pattern of the pressed button.
The detector on the TV will be pre-programmed to interpret the binary codes and perform the requested actions. These binary codes vary from company to company and device to device, which is why we can't control a TV with a remote that doesn't belong to it. Although, a universal remote has all the codes programmed into it, which is why it can control any TV.
If there is some object between your remote and the TV, the detector on the TV might not be able to get the Infrared rays from the remote as these rays can't penetrate through objects. New technology led to various changes in Remote control, like using Radio waves instead of Infrared, mobile apps, voice control, etc.
Other Applications of Infrared transmissions:
- Laptops to printers
- Development of high-speed LANs
- Cordless microphones, headsets
- LASER communications
- Modems, robot control systems, etc.
Advantages of Infrared communication:
- Large bandwidth
- Simple and inexpensive to implement
- The best medium for short-range communication
- Secure transmission
- Risks of interception and interference are low
- Power usage is efficient
Disadvantages of Infrared communication:
- Due to its Line of sight propagation, the transmitter needs to be aligned with the receiver to transmit the data.
- Only short-range communication is supported.
- It can't propagate through obstructions like walls, wood, and other opaque objects.
- Some receivers might respond to other transmitters breaking the security policy.
- High interference rate due to sunlight and other large Infrared sources.
2. Radio waves
Like Infrared radiation, Radio waves are also a part of electromagnetic radiation. These waves have the longest wavelengths, from 1mm to 100km in the spectrum. The name itself has Radio. A Radio is one of the thousands of wireless technologies that use Radio waves for communication.
A Radio is the simplest example of Radio wave communication. Other examples include RADAR, Satellite communications, Bluetooth headsets, TV Broadcasts, GPS Signals, etc. Frequency range: 300GHz to 3kHz.
Like in Infrared communication, there will be a Radio wave transmitter and a receiver. All the Radios today use continuous sine waves to transmit information, as almost every single person on the planet uses these waves in one form or another. The information can be from audio, video, sound, and textual data. Suppose a person is using Radio, sine waves are transmitted from it, and if another person uses a TV, it also broadcasts sine waves. How are these signals separated and identified? Every single Radio signal will have a different frequency for the sine waves.
A Radio station is an equipment installation with one or more transmitters or receivers.
This is the flow:
Transmitter (Sender's side):
- Information -> Sine waves -> Radio waves -> Antenna
The information in any form is encoded into sine waves and is transmitted into the air by radiating the waves through an Antenna.
Receiver (Destination):
- Antenna -> Radio waves -> Sine waves
The Antenna on the receiver's side captures the Radio waves and decodes the information from the sine waves.
To transmit Radio signals, there is a need for a transmitting antenna on the transmitter's side and a receiving antenna at the receiver's side.
There is a concept to understand here:
- The frequency of a wave is inversely proportional to wavelength, and the length of the Antenna is directly proportional to the wavelength of the wave.
Let us take an example of a sound wave. The frequency range a human ear can sense is 20Hz to 20kHz. If we try to transmit the Radio wave at the same frequency as the sound waves, the length of the antennas required will be in kilometers. It is not feasible.
Here comes the concept of Modulation.
We need the antenna height to be low, which means we need the Radio wave with high frequency. Hence, a signal with high frequency is taken, and its characteristics (amplitude or frequency, phase or pulse) are altered to store the information.
After the modulation process, we'll get a high-frequency wave with all the data encoded into the wave. This wave is transmitted to the receiver Radio station, and demodulation is done to extract the blended data.
Observe that there are FM Radios, AM Radios, and PM Radios based on the type of Modulation the Radio wave is going through to carry the information.
Here is an example of Frequency Modulation:
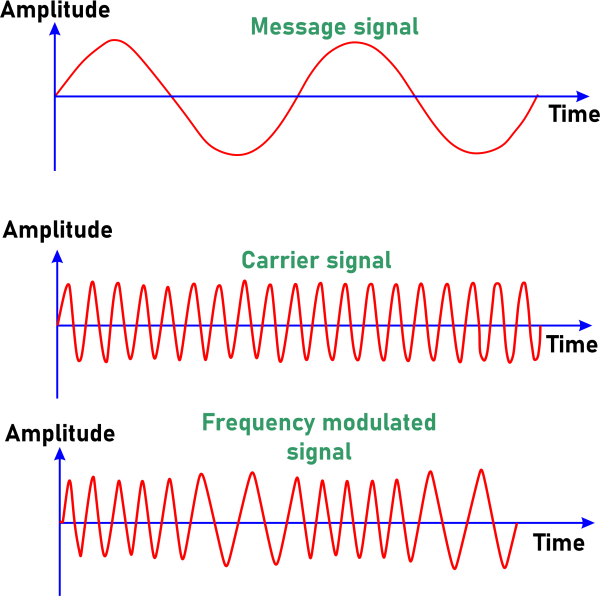
The first wave is the message the Transmitter wants to send. The next wave is a new signal with high frequency with no data in it. Now, the carrier signal is modified in terms of its frequency to carry the data in the message signal like a Morse code. This data will be demodulated to get back the message at the receiver's side.
Advantages:
- Radio waves are the best choice for large-distance communications.
- These waves can also penetrate through obstacles.
- These waves are Omnidirectional which means they can be transmitted in all directions.
- Low cost.
Disadvantages:
- Not very secure due to the large distances
- Interference with other Radio signals
- Not very effective in bad weather conditions.
3. Microwaves
These waves are also a part of electromagnetic radiation. The micro indicates that these waves have short wavelengths from 1 meter to 1 millimeter. These are high-frequency waves-> Frequency range: 300MHz to 300GHz. These waves fall between Radio waves and Infrared waves.
These waves are used for point-to-point communication as it only transmits data in one direction. These can transmit all kinds of data, from audio to video. These waves can be used to transmit thermal energy too.
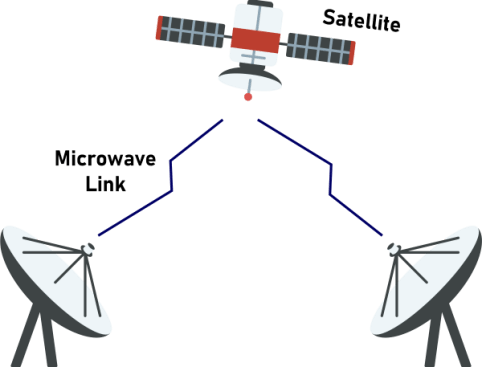
Communication using Microwaves can be done only if the transmitting and receiving antennas are properly aligned- Line of sight transmission.
Applications:
- Cooking food in Microwave ovens, Popcorn machines.
- TV distributions
- Capturing the speed of the vehicle
- Phone channels to a mobile phone
- RADAR, Satellite communications
Advantages:
- The speed of transmission is very fast
- We can reduce antenna size due to high frequency
- Lower power consumption
- Supports larger bandwidth
- Can easily pass through the Ionosphere.
Disadvantages:
- Expensive
- Not effective in bad weather conditions
- Occupies more space
- Interference
- Harmful radiation


