Tutorial
Physical Layer
Data Link layer
Network Layer
Routing Algorithm
Transport Layer
Application Layer
Network Security
Misc
- Router
- OSI vs TCP/IP
- TCP vs UDP
- Transmission Control Protocol
- TCP port
- IPv4 vs IPv6
- ARP Packet Format
- ARP Table
- Working of ARP
- FTP Client
- FTP Commands
- FTP Server
- I2C Protocol
- Sliding Window Protocol
- SPI Protocol
- IP
- ARP Commands
- ARP
- Address Resolution Protocol
- ARP and its types
- TCP Retransmission
- CAN protocol
- HTTP Status Codes
- HTTP vs HTTPS
- RIP Protocol
- UDP Protocol
- ICMP Protocol
- MQTT protocol
- OSPF Protocol
- Stop and Wait Protocol
- IMAP Protocol
- POP Protocol
- CIFS
- DAS
- DIMM
- iSCSI
- NAS (Network Attached Storage)
- NFS
- NVMe
- SAN
- Border Gateway Protocol
- Go-Back-N ARQ
- RJ Cable
- Difference between Connection-Oriented and Connectionless Service
- CDMA vs. GSM
- What is MAC Address
- Modem vs. Router
- Switch Vs. Router
- USB 2.0 vs 3.0
- Difference between CSMA CA and CSMA CD
- Multiple access protocol- ALOHA, CSMA, CSMA/CA and CSMA/CD
- URI vs URL
- IMAP vs. POP3
- SSH Meaning| SSH Protocol
- UTP vs STP
- Status Code 400
- MIME Protocol
- IP address
- proxy server
- How to set up and use a proxy server
- network security
- WWW is based on which model
- Proxy Server List
- Fundamentals of Computer Networking
- IP Address Format and Table
- Bus topology and Ring topology
- Bus topology and Star topology
- Circuit Switching and Packet switching?
- Difference between star and ring topology
- Difference between Router and Bridge
- TCP Connection Termination
- Image Steganography
- Network Neutrality
- Onion Routing
- Adaptive security appliance (ASA) features
- Relabel-to-front Algorithm
- Types of Server Virtualization in Computer Network
- Access Lists (ACL)
- What is a proxy server and how does it work
- Digital Subscriber Line (DSL)
- Operating system based Virtualization
- Context based Access Control (CBAC)
- Cristian's Algorithm
- Service Set Identifier (SSID)
- Voice over Internet Protocol (VoIP)
- Challenge Response Authentication Mechanism (CRAM)
- Extended Access List
- Li-fi vs. Wi-fi
- Reflexive Access List
- Synchronous Optical Network (SONET)
- Wifi protected access (WPA)
- Wifi Protected Setup (WPS)
- Standard Access List
- Time Access List
- What is 3D Internet
- 4G Mobile Communication Technology
- Types of Wireless Transmission Media
- Best Computer Networking Courses
- Data Representation
- Network Criteria
- Classful vs Classless addressing
- Difference between BOOTP and RARP in Computer Networking
- What is AGP (Accelerated Graphics Port)
- Advantages and Disadvantages of Satellite Communication
- External IP Address
- Asynchronous Transfer Mode (ATM)
- Types of Authentication Protocols
- What is a CISCO Packet Tracer
- BOOTP work
- Subnetting in Computer Networks
- Mesh Topology Advantages and Disadvantages
- Ring Topology Advantages and Disadvantages
- Star Topology Advantages and Disadvantages
- Tree Topology Advantages and Disadvantages
- Zigbee Technology-The smart home protocol
- Network Layer in OSI Model
- Physical Layer in OSI Model
- Data Link Layer in OSI Model
- Internet explorer shortcut keys
- Network Layer Security | SSL Protocols
- Presentation Layer in OSI Model
- Session Layer in OSI Model
- SUBNET MASK
- Transport Layer Security | Secure Socket Layer (SSL) and SSL Architecture
- Functions, Advantages and Disadvantages of Network Layer
- Protocols in Noiseless and Noisy Channel
- Advantages and Disadvantages of Mesh Topology
- Cloud Networking - Managing and Optimizing Cloud-Based Networks
- Collision Domain and Broadcast Domain
- Count to Infinity Problem in Distance Vector Routing
- Difference Between Go-Back-N and Selective Repeat Protocol
- Difference between Stop and Wait, GoBackN, and Selective Repeat
- Network Function Virtualization (NFV): transforming Network Architecture with Virtualized Functions
- Network-Layer Security | IPSec Modes
- Next - Prev Network-Layer Security | IPSec Protocols and Services
- Ping vs Traceroute
- Software Defined Networking (SDN): Benefits and Challenges of Network Virtualization
- Software Defined Networking (SDN) vs. Network Function Virtualization (NFV)
- Virtual Circuits vs Datagram Networks
- BlueSmack Attack in Wireless Networks
- Bluesnarfing Attack in Wireless Networks
- Direct Sequence Spread Spectrum
- Warchalking in Wireless Networks
- WEP (Wired Equivalent Privacy)
- Wireless security encryption
- Wireless Security in an Enterprise
- Quantum Networking
- Network Automation
- Difference between MSS and MTU
- What is MTU
- Mesh Networks: A decentralized and Self-Organizing Approach to Networking
- What is Autonomous System
- What is MSS
- Cyber security & Software security
- Information security & Network security.
- Security Engineer & Security Architect
- Protection Methods for Network Security
- Trusted Systems in Network Security
- What are Authentication Tokens in Network security
- Cookies in Network Security
- Intruders in Network Security
- Network Security Toolkit (NST) in virtual box
- Pivoting-Moving Inside a Network
- Security Environment in Computer Networks
- Voice Biometric technique in Network Security
- Advantages and Disadvantages of Conventional Testing
- Difference between Kerberos and LDAP
- Cyber security and Information Security
- GraphQL Attacks and Security
- Application Layer in OSI Model
- Applications of Remote Sensing
- Seven Layers of IT Security
- What is Ad Hoc TCP
- What is Server Name Indication(SNI)
Onion Routing
Onion routing is a method of communicating anonymously over a computer network. Messages in an onion network are encapsulated in layers of encryption, similar to the layers of an onion.
To make web browsing safer and more secure for users, there is a large set of precautionary measures and best practises. Assume you send an HTTPS request to a server and someone intercepts it, but that person cannot read the message because it is encrypted. However, you are not satisfied with this level of security and wish to take it to the next level, i.e. you do not want anyone sniffing on your network to know which server you are contacting and whether or not you are making any requests. This is where the onion routing comes into play.
The Onion Routing programme is made up of studies that look into, design, build, and analyse anonymous communication networks. The emphasis is on practical solutions for low-latency Internet-based connections that can withstand traffic analysis, eavesdropping, and other attacks from both outsiders (like Internet routers) and insiders (like hackers) (Onion Routing servers themselves). The network only knows that communication is taking place because onion routing hides who is communicating with whom from the transport medium. Furthermore, the content of the conversation is hidden from eavesdroppers until the transmission leaves the OR network.
What is the procedure for onion routing?
When you browse the internet using a standard web browser such as Chrome or Firefox, you request webpages by sending simple GET requests to servers with no intermediary. It is only a single connection between a client and a server, and anyone sniffing on your network can determine which server your computer is contacting.
- This is done differently in onion routing. The connection is maintained between different nodes in onion routing, i.e. the connection hops from one server to another and when it reaches the last server on this circuit, it is the server that we wanted to contact and it will process our request and serve us the desired webpage, which is returned to us using the same network of nodes.
- You're probably wondering why it's called the onion router. It's because the messages we send and the responses we receive are encrypted with different keys, with each hop or server visit requiring a different key for encryption.
- The client has access to all keys, but the servers only have access to the keys that are specific to that server's encryption/decryption.
- Because this process wraps your message in layers of encryption that must be peeled off at each different hop, it is referred to as an onion router.
An explanation of the onion routing concept
Now imagine you are using Tor (the onion router), a unique browser that enables you to use the onion routers, to browse the internet. Since YouTube is blocked in China, you want to access YouTube but you also don't want your government to find out that you are doing so, so you choose to use Tor. To get the YouTube homepage, your computer must make contact with a specific server, but it does not do so directly. In order to prevent anyone from tracking the conversation you had with that server, it does this through three nodes/servers/routers (maintained by volunteers around the world) before that server. Although a real Tor network can have hundreds of nodes in between, I am only using 3 nodes in this example to keep things simple.
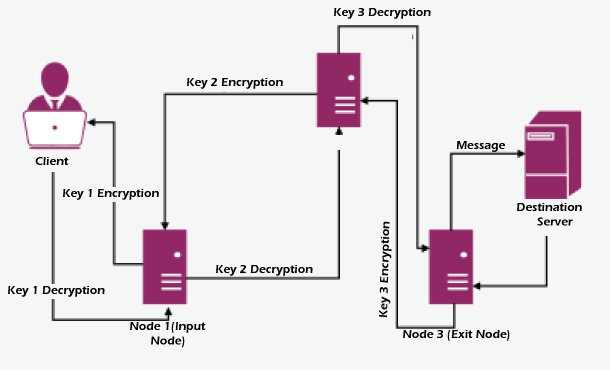
- The client encrypts the message (get request) three times, wrapping it in three layers like an onion that must be peeled one layer at a time. This client has access to keys 1, 2, and 3.
- This triple-encrypted message is then forwarded to Node 1, the first server (Input Node).
- Only Node 2's address and Key 1 are stored in Node 1. It uses Key 1 to decrypt the message but realises that it is illogical because there are still two layers of encryption, so it sends the message to Node 2.
- Key 2 and the addresses of the input and exit nodes are located on Node 2. It then transmits the message to the exit node after using Key 2 to decrypt it but realising that it is still encrypted.
- A GET request for youtube.com is discovered by Node 3 (the exit node), which removes the final layer of encryption and forwards it to the target server.
- The requested webpage is delivered as a result of the server processing the request.
- The response travels backwards through the same nodes, each of which adds a layer of encryption using its unique key.
- In the end, it is delivered to the client as a triple encrypted response that can be decrypted because the client has access to all the keys.
In what way does it offer anonymity?
Imagine that a sniffer is present at the first connection (client - input node) and that all it can decipher is the address of the input node and an illogical message that has been triple encrypted. Therefore, the spy or attacker is aware that you are using Tor to browse.
Similar to this, if sniffing begins at the exit node, all the sniffer sees is one server speaking to another, but it is unable to identify the client or the origin of the request.
However, you might now imagine that if someone were to listen in at Node 2, they would be able to trace the client and the destination server if they knew the addresses of the input and exit. But it's not that easy; each of these nodes is running hundreds of connections simultaneously, making it difficult to determine which connection leads to the correct source and destination. Node 2 is a middle node in our circuit, but it can also be a part of another circuit on a different connection where it serves as an exit node dispensing websites from various servers or an input node receiving requests.
Attack Surface for Onion Routing
The only security hole in onion routing is that if someone is watching a server at the same time and compares a request made by a client on the other side of the network to a request made by a server at the destination by analysing the length and frequency of the characters found in the intercepted request or response at the destination server and using that to match with the same request made by a client in a split second (time-stamps on requests and responses can also be used as a substitute for Even though it's challenging, it's not impossible. However, fixing this flaw in Tor is essentially impossible.


