Tutorial
Physical Layer
Data Link layer
Network Layer
Routing Algorithm
Transport Layer
Application Layer
Network Security
Misc
- Router
- OSI vs TCP/IP
- TCP vs UDP
- Transmission Control Protocol
- TCP port
- IPv4 vs IPv6
- ARP Packet Format
- ARP Table
- Working of ARP
- FTP Client
- FTP Commands
- FTP Server
- I2C Protocol
- Sliding Window Protocol
- SPI Protocol
- IP
- ARP Commands
- ARP
- Address Resolution Protocol
- ARP and its types
- TCP Retransmission
- CAN protocol
- HTTP Status Codes
- HTTP vs HTTPS
- RIP Protocol
- UDP Protocol
- ICMP Protocol
- MQTT protocol
- OSPF Protocol
- Stop and Wait Protocol
- IMAP Protocol
- POP Protocol
- CIFS
- DAS
- DIMM
- iSCSI
- NAS (Network Attached Storage)
- NFS
- NVMe
- SAN
- Border Gateway Protocol
- Go-Back-N ARQ
- RJ Cable
- Difference between Connection-Oriented and Connectionless Service
- CDMA vs. GSM
- What is MAC Address
- Modem vs. Router
- Switch Vs. Router
- USB 2.0 vs 3.0
- Difference between CSMA CA and CSMA CD
- Multiple access protocol- ALOHA, CSMA, CSMA/CA and CSMA/CD
- URI vs URL
- IMAP vs. POP3
- SSH Meaning| SSH Protocol
- UTP vs STP
- Status Code 400
- MIME Protocol
- IP address
- proxy server
- How to set up and use a proxy server
- network security
- WWW is based on which model
- Proxy Server List
- Fundamentals of Computer Networking
- IP Address Format and Table
- Bus topology and Ring topology
- Bus topology and Star topology
- Circuit Switching and Packet switching?
- Difference between star and ring topology
- Difference between Router and Bridge
- TCP Connection Termination
- Image Steganography
- Network Neutrality
- Onion Routing
- Adaptive security appliance (ASA) features
- Relabel-to-front Algorithm
- Types of Server Virtualization in Computer Network
- Access Lists (ACL)
- What is a proxy server and how does it work
- Digital Subscriber Line (DSL)
- Operating system based Virtualization
- Context based Access Control (CBAC)
- Cristian's Algorithm
- Service Set Identifier (SSID)
- Voice over Internet Protocol (VoIP)
- Challenge Response Authentication Mechanism (CRAM)
- Extended Access List
- Li-fi vs. Wi-fi
- Reflexive Access List
- Synchronous Optical Network (SONET)
- Wifi protected access (WPA)
- Wifi Protected Setup (WPS)
- Standard Access List
- Time Access List
- What is 3D Internet
- 4G Mobile Communication Technology
- Types of Wireless Transmission Media
- Best Computer Networking Courses
- Data Representation
- Network Criteria
- Classful vs Classless addressing
- Difference between BOOTP and RARP in Computer Networking
- What is AGP (Accelerated Graphics Port)
- Advantages and Disadvantages of Satellite Communication
- External IP Address
- Asynchronous Transfer Mode (ATM)
- Types of Authentication Protocols
- What is a CISCO Packet Tracer
- BOOTP work
- Subnetting in Computer Networks
- Mesh Topology Advantages and Disadvantages
- Ring Topology Advantages and Disadvantages
- Star Topology Advantages and Disadvantages
- Tree Topology Advantages and Disadvantages
- Zigbee Technology-The smart home protocol
- Network Layer in OSI Model
- Physical Layer in OSI Model
- Data Link Layer in OSI Model
- Internet explorer shortcut keys
- Network Layer Security | SSL Protocols
- Presentation Layer in OSI Model
- Session Layer in OSI Model
- SUBNET MASK
- Transport Layer Security | Secure Socket Layer (SSL) and SSL Architecture
- Functions, Advantages and Disadvantages of Network Layer
- Protocols in Noiseless and Noisy Channel
- Advantages and Disadvantages of Mesh Topology
- Cloud Networking - Managing and Optimizing Cloud-Based Networks
- Collision Domain and Broadcast Domain
- Count to Infinity Problem in Distance Vector Routing
- Difference Between Go-Back-N and Selective Repeat Protocol
- Difference between Stop and Wait, GoBackN, and Selective Repeat
- Network Function Virtualization (NFV): transforming Network Architecture with Virtualized Functions
- Network-Layer Security | IPSec Modes
- Next - Prev Network-Layer Security | IPSec Protocols and Services
- Ping vs Traceroute
- Software Defined Networking (SDN): Benefits and Challenges of Network Virtualization
- Software Defined Networking (SDN) vs. Network Function Virtualization (NFV)
- Virtual Circuits vs Datagram Networks
- BlueSmack Attack in Wireless Networks
- Bluesnarfing Attack in Wireless Networks
- Direct Sequence Spread Spectrum
- Warchalking in Wireless Networks
- WEP (Wired Equivalent Privacy)
- Wireless security encryption
- Wireless Security in an Enterprise
- Quantum Networking
- Network Automation
- Difference between MSS and MTU
- What is MTU
- Mesh Networks: A decentralized and Self-Organizing Approach to Networking
- What is Autonomous System
- What is MSS
- Cyber security & Software security
- Information security & Network security.
- Security Engineer & Security Architect
- Protection Methods for Network Security
- Trusted Systems in Network Security
- What are Authentication Tokens in Network security
- Cookies in Network Security
- Intruders in Network Security
- Network Security Toolkit (NST) in virtual box
- Pivoting-Moving Inside a Network
- Security Environment in Computer Networks
- Voice Biometric technique in Network Security
- Advantages and Disadvantages of Conventional Testing
- Difference between Kerberos and LDAP
- Cyber security and Information Security
- GraphQL Attacks and Security
- Application Layer in OSI Model
- Applications of Remote Sensing
- Seven Layers of IT Security
- What is Ad Hoc TCP
- What is Server Name Indication(SNI)
What is MTU
MTU stands for maximum transmission unit in computer networking. It refers to the largest data frame or packet that can be transferred between the nodes using the connection. The size of the frame or the packet is computed in bytes or octets, where one octet is an eight-bit byte. This term is widely used to represent the packet size in an Ethernet connection implemented using the Internet Protocol. However, there is a difference between MTU and maximum frame size.
The greater maximum transmission unit is related to the reduced overhead. At the same time, if the MTU value is less, it can reduce the delay in transmission in the network. In most scenarios, MTU is determined by the underlying network capacity. It should be managed either manually or automatically so that it does not surpass the network's capacity.
Some nodes can adjust the maximum transmission unit when connecting with the other node. This is done by using Path MTU Discovery. MTU parameters may be represented with the communications interface or standard.
Application of MTU
- MTU is used in network layer protocols and other protocols associated with communications. The MTU is described in bytes or octets of the largest protocol data unit that the network layer can further transmit.
- MTU parameters are specified with the communication interface in the network, that is, serial port or NIC. The transmission standards such as Ethernet can define the size of the MTU. Nodes can also determine the size of MTU during the connection.
- The data link and the physical layers in the network usually increase the overhead in the network layer data to be transmitted. So if the user is provided with the maximum frame size of the data transmitted in the network, then the user must subtract the amount of overhead to compute the maximum transmission unit of the data.
- For instance, if the user uses an Ethernet connection, the maximum frame size is 1518 bytes, where the MTU is 1500 bytes only, and the rest of the 18 bytes are the overhead data added by the network layers to the data frame. This includes components such as headers and checks sequence numbers.
MTU and Packet Fragmentation in the Network
Each node in the network has a limit to the maximum transmission unit size that can be transmitted or received by that node in the network. The node determines the MTU of the next receiving node in the network before sending the data frame to that node. This is done to ensure that the packet size is not larger than the MTU of the node. If it is larger, then it won't accept the data frame. Thus, the packet is first divided into smaller parts. The process is known as fragmentation of the data frame.
Though performing fragmentation is not ideal as it reduces the performance of data transmission by adding delay and overhead data to the data, to ensure the best performance of the network, the MTU of the original transmitting node should be kept as high as possible; the value should be still less than the MTU of all the nodes connected in the network that are connected between the sender and final receiving node in the network. It is impossible to set these values automatically the first time because the sender node does not know the maximum transmission node for all the nodes in the network. The sender node only knows the MTU of the next node in the transmission.
The user can think of MTU as the maximum weight that can be transported as a single package. Consider if an organization wants to transfer 1000 kg of goods to another location. The goods are initially stored in a warehouse with trucks that can be used to deliver the goods. The complete shipment is packed into a single package and delivered as a single package. This is similar to transmitting the data between the nodes with a large MTU where all the nodes should support the MTU. It is very efficient as there is no requirement to instruct multiple transporters with information.
Now consider another example where the organization needs to transport the same amount of goods to a smaller organization. The smaller organization lacks resources to transport the resources. They can only accept the goods from a mail carrier that has a small van. If the company sends the entire order through a single large package, the organization would have to split this larger package into smaller boxes to be transported further in the smaller van and delivered to the smaller organization. This is similar to the scenario where the sender node only supported the larger MTU, which is too much to handle by the receiver or intermediary node. The more appropriate approach will be where the MTU is determined by the original sender, in this case, the bigger organization, such that it can be supported by all the intermediary nodes rather than performing fragmentation at an intermediate load. This will be more efficient as the overhead will be added once during transmission. Moreover, it may be possible that fragmentation will be performed by multiple intermediary nodes, reducing the transmission performance.
Packet fragmentation is only possible in Internet Protocol Version 4.0 (IPv4). Suppose the sender node transmits a data packet larger than the MTU over IPv4. The protocol automatically performs fragmentation of the data packet. This step is not performed if the data packet has a do-not-fragment flag set. The IPv6 protocol does not support fragmentation. If a packet larger than MTU is detected in the network, it is dropped from the network.
Types of Maximum Transmission Units
Ethernet Maximum Transmission Unit (EMTU)
The Ethernet frame is in the data link layer of the OSI model. It is the second layer in Open System Interconnection. The standard size of the Ethernet maximum transmission unit is 1500 bytes. The maximum frame size transmitted using Ethernet is 1518-1520. This 18-20 bytes of data comprises the header and additional overhead of the data frame. It is also theoretically the maximum size of the data frame that can be transferred using a physical cable. The MTU from any higher-level protocols must range within the standard MTU. If the data frame size exceeds the MTU, then it can't be transmitted by the Ethernet.
Internet Protocol Maximum Transmission Unit (IP MTU)
The Internet Protocol is implemented in the third layer of the Open System Interconnection. The size of the IP MTU packet can be determined independently of the size of the Ethernet frame. The size of the IP MTU must be smaller than the size of the Ethernet frame because, in the end, the data frame is transmitted using the Ethernet cable. The IP MTU comprises the size of the data frame and the overhead data. It includes the header and the data payload transmitted with the frame. The size of the TCP/IP header is about 40 bytes.
Returning to the analogy, consider the maximum weight the forklift can lift is 1500 kg. And the size of each package is 70 kg. Then the maximum weight that can be loaded on the forklift will be 1470 kg. Adding one more package will exceed the maximum limit of the forklift.
Suppose the network implements an additional intermediary protocol during data frame transmission. Some protocols implemented between transmissions are GRE, SNAP or IPsec. However, these protocols are not included in the maximum transmission unit of the sender. It is necessary to consider the data from these protocols during the transmission. The user must include them during the network design to ensure that this does not exceed the maximum transmission unit of the intermediary nodes in the network.
This protocol will add additional data to the data frame required to perform encryption on the data frame. Additional data will be added to the data frame. This additional data contains information about encryption. This increases the size of the data packet, ultimately exceeding the 1500-byte limit. For instance, if an institution fixes the maximum transmission unit size to 1500 bytes, it must transmit the data frame over a virtual private network that IPsec secures. Thus, the packet can no longer be transmitted through an Ethernet cable. Therefore, the packet is fragmented before transmission.
To understand the above concept, consider the following analogy in which there is a warehouse that requires to keep safe the goods stored in the warehouse. They decide to store the entire shipment in a locked safe. If the weight of the locked safe used for storing the shipment is not taken into account, the total weight of the goods (data payload), pallet (header and flags), and the locked safe(IPsec) can exceed the total weight that the forklift can handle. Here forklift capacity represents the MTU of the node.
Maximum Segment Size and Maximum Transmission Unit
The packet is the data the sender node wants to transmit to the receiver node. It is the most data that the sender node can transmit in a single data packet without exceeding the MTU of the node. The maximum segment size represents the maximum size of the data payload in a data packet.
The user can compute the MSS by subtraction the header size from the IP MTU. The IP MTU is on the Layer 4 of the Open System Interconnection model.
Jumbo Frames and MTU
Jumbo frames are when the Ethernet MTU is more than the standard 1500 bytes. This is possible when the nodes are connected using fast Ethernet cables. If the user uses a Gigabit LAN, it increases the MTU to almost 9000 bytes. This is useful when you have reliable connections. This reduces the overhead by transmitting a larger volume of data as a single packet. It increases the efficiency of data transmission in the network.
The size of the jumbo packet depends on the vendor. The jumbo frames are not guaranteed to be used over the internet. Therefore, these frames are avoided during transmission over the internet and are used to transmit data in a dedicated specialized network that ensures frame delivery. An example of this network is a storage area network (SAN). Since a large volume of data is handled in this network, using jumbo frames to optimize network performance is beneficial.
Determining the MTU of All Nodes
- Path Maximum Transmission unit discovery (PMTUD) refers to determining the maximum transmission unit for all the nodes transversed by the data frame en route from the sender to the receiver. It is used to avoid frequent fragmentation of frames by the different nodes. It also prevents dropping data frames in the network where fragmentation is not supported. It is important to perform PMTUD in the network when multiple intermediary nodes are present to deliver the data packet. This may occur when the frame size exceeds the intermediary nodes' MTU.
- The easiest way to determine the MTU of a node is by sending large test data packets or pings set to not fragment. This ensures that fragmentation is not performed on the data frame. When the packet is dropped, it means the size of the packet is more than the node MTU. Thus, the size of the packet is decreased until it reaches the final node, and if the packets are successfully transmitted to the network, it sends the packet with a larger size. It is one of the methods to perform path MTU discovery.
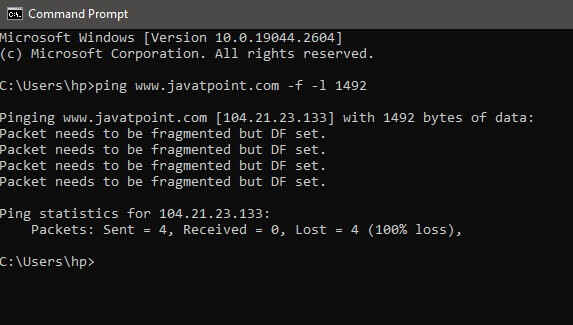
- In the windows operating system, the user can determine the MTU of the node by using the ping command in the command prompt. The user can use the -f and -l switches to find the MTU. -f switch represents the do not fragment flag, while -l determines the data packet size in bytes that will be transmitted in the network. For example: ping javatpoint.com-f -l 1492
Optimizing Maximum Transmission Units
- There is no standard best size that could be assigned for IP MTU. The user cannot set any particular value for all the nodes in the network. The maximum transmission unit is determined by the node and the protocols implemented in the node during the data transmission. This may vary between different nodes. Thus, it varies for different nodes in the network. This is another reason why the user must be careful while adjusting the endpoint MTU. Most nodes in the network can compute the MTU and adjust it accordingly to transfer the data to the next node. It depends on the type of connection and the network the two nodes use for communication.
- The most optimal value for the maximum transmission unit is closest to the lowest MTU value in the routing path. It is ensured that the optimal MTU value does not exceed the lowest MTU value of the node. If the user already knows particular constraints, then it is better to reduce the value of the MTU.
- For instance, if the user knows that the nodes in the organization use IPsec and VPN protocols, the user needs to set the MTU of the node to account for the overhead data that will be added because of the implementation of the given protocols. If not considered, it may increase the packet fragmentation in the network as the size after adding overhead may exceed the MTU. Certain internet service protocol technologies, such as ADSL, can add overhead data to the packet. It reduces the endpoint node MTU; so that it can ensure efficient performance.
Internet Protocol and its Effect on MTU
- The Internet Protocol Suite was developed to be implemented over different network technologies. The different network technologies have different requirements and can use data packets of different sizes to transmit the data in the network. The host can determine the MTU of its node and compute the MTU of the peer node when performing the initial handshake. The host node does not know the lowest MTU in a network with multiple intermediary nodes. The nodes can compute the MTU for the next node in the routing path. Another issue lies with implementing higher-level protocols in the language, as they may add large data overhead to the data packet, increasing the size of the data packet to that supported by the local connection connecting the nodes.
- Internet protocol version 4 (IPV4) allows the node to fragment the data packet, which enables the node to split the datagram into smaller units. The size of each unit is such that it can be adjusted to a specified MTU limitation. This fragmentation function on the data frame is performed at the internet layer. The protocol marks the fragmented data packets to ensure that the IP layer knows the address of the destination node. As the datagram reaches the destination node, the fragmented datagram is reassembled to form the original datagram.
- Suppose the number of data packets is fragmented or the number of data packets increases significantly after performing fragmentation on the data. In that case, the additional data added to each fragmented packet can create large unnecessary data overhead in the network.
- To understand this problem, consider an example where several packets have crossed the maximum transmission unit by a very small margin. This increase is due to the additional data provided in the data packet's header. Though this additional data is very small, the data packets will still be required to be fragmented. Thus, each data packet will be split into two smaller parts, and the actual data, the data payload in the second fragment, will be very small. The same data is transmitted in the network. It means moving the same amount of data in the network. Each network router will have to send twice as many data packets into the network. It increases the traffic in the network.
- To be a host to implement the Internet Protocol should be able to handle the IP datagram of at least 576 bytes to implement the IP version 4 or 1280 bytes to implement the IPv6 protocol in the network. This datagram size does not preclude the network layer with MTU smaller than the MTU mentioned above from transmitting the IP data.
- For instance, in IPv6, if a specific link layer cannot transmit the IP datagram of 1280 bytes as a single unit, then it is the responsibility of the link layer to perform fragmentation on the frame and provide a reassembling mechanism at the sender node. It is essential to provide fragmentation and assembly mechanisms to ensure that the transmitted data is rearranged and delivered correctly.
Disadvantages of Using Larger MTU
- The greater the value of the MTU, the more efficient the data transmission will be. It is because more data can be transmitted as a single unit in the network. It means that the number of data packets will be less to transmit the data in the network. Each data packet carries the same data and protocol overhead that stores data such as header. The increased data transmission efficiency means improved data transmission in bulk protocol throughput. It also means that there will be fewer data packets to be routed in the network to carry the same data. Some systems can process a fixed number of data packets. Thus, fewer data packets mean increased processing power in a system that can process a fixed number of data packets.
- There is a disadvantage to larger MTU as well. The larger the data packet being transferred will occupy the link for more time. This slows down the entire network. The smaller data packet is transported quickly in the network. This results in greater delays for the next data packets. It can cause network delay and delay variation in the network. For instance, if the nodes transmit the largest data packet possible that can be transferred via Ethernet cable in the network, that is 1500 byte data packet. It requires a 14.4k modem to transmit it further in the network for a whole second.
- Large packets also cause an issue if a communication error occurs during the data transmission. If no forward correction is implemented in the network, the entire data packet will have to be re-transmitted, even if only one bit of data is corrupted. This increases the network cost.
- For any bit error rate in the network, the data packets with larger MTU are more likely to be corrupted. The greater data payload makes the retransmission of these packets take more time. Despite the above negative effects of the
- Larger packets are more susceptible to corruption at a given bit error rate. Their greater payload makes retransmissions of larger packets take longer. Despite the negative effects on retransmission duration, large packets can still have a net positive effect on end-to-end TCP performance.


