Tutorial
Physical Layer
Data Link layer
Network Layer
Routing Algorithm
Transport Layer
Application Layer
Network Security
Misc
- Router
- OSI vs TCP/IP
- TCP vs UDP
- Transmission Control Protocol
- TCP port
- IPv4 vs IPv6
- ARP Packet Format
- ARP Table
- Working of ARP
- FTP Client
- FTP Commands
- FTP Server
- I2C Protocol
- Sliding Window Protocol
- SPI Protocol
- IP
- ARP Commands
- ARP
- Address Resolution Protocol
- ARP and its types
- TCP Retransmission
- CAN protocol
- HTTP Status Codes
- HTTP vs HTTPS
- RIP Protocol
- UDP Protocol
- ICMP Protocol
- MQTT protocol
- OSPF Protocol
- Stop and Wait Protocol
- IMAP Protocol
- POP Protocol
- CIFS
- DAS
- DIMM
- iSCSI
- NAS (Network Attached Storage)
- NFS
- NVMe
- SAN
- Border Gateway Protocol
- Go-Back-N ARQ
- RJ Cable
- Difference between Connection-Oriented and Connectionless Service
- CDMA vs. GSM
- What is MAC Address
- Modem vs. Router
- Switch Vs. Router
- USB 2.0 vs 3.0
- Difference between CSMA CA and CSMA CD
- Multiple access protocol- ALOHA, CSMA, CSMA/CA and CSMA/CD
- URI vs URL
- IMAP vs. POP3
- SSH Meaning| SSH Protocol
- UTP vs STP
- Status Code 400
- MIME Protocol
- IP address
- proxy server
- How to set up and use a proxy server
- network security
- WWW is based on which model
- Proxy Server List
- Fundamentals of Computer Networking
- IP Address Format and Table
- Bus topology and Ring topology
- Bus topology and Star topology
- Circuit Switching and Packet switching?
- Difference between star and ring topology
- Difference between Router and Bridge
- TCP Connection Termination
- Image Steganography
- Network Neutrality
- Onion Routing
- Adaptive security appliance (ASA) features
- Relabel-to-front Algorithm
- Types of Server Virtualization in Computer Network
- Access Lists (ACL)
- What is a proxy server and how does it work
- Digital Subscriber Line (DSL)
- Operating system based Virtualization
- Context based Access Control (CBAC)
- Cristian's Algorithm
- Service Set Identifier (SSID)
- Voice over Internet Protocol (VoIP)
- Challenge Response Authentication Mechanism (CRAM)
- Extended Access List
- Li-fi vs. Wi-fi
- Reflexive Access List
- Synchronous Optical Network (SONET)
- Wifi protected access (WPA)
- Wifi Protected Setup (WPS)
- Standard Access List
- Time Access List
- What is 3D Internet
- 4G Mobile Communication Technology
- Types of Wireless Transmission Media
- Best Computer Networking Courses
- Data Representation
- Network Criteria
- Classful vs Classless addressing
- Difference between BOOTP and RARP in Computer Networking
- What is AGP (Accelerated Graphics Port)
- Advantages and Disadvantages of Satellite Communication
- External IP Address
- Asynchronous Transfer Mode (ATM)
- Types of Authentication Protocols
- What is a CISCO Packet Tracer
- BOOTP work
- Subnetting in Computer Networks
- Mesh Topology Advantages and Disadvantages
- Ring Topology Advantages and Disadvantages
- Star Topology Advantages and Disadvantages
- Tree Topology Advantages and Disadvantages
- Zigbee Technology-The smart home protocol
- Network Layer in OSI Model
- Physical Layer in OSI Model
- Data Link Layer in OSI Model
- Internet explorer shortcut keys
- Network Layer Security | SSL Protocols
- Presentation Layer in OSI Model
- Session Layer in OSI Model
- SUBNET MASK
- Transport Layer Security | Secure Socket Layer (SSL) and SSL Architecture
- Functions, Advantages and Disadvantages of Network Layer
- Protocols in Noiseless and Noisy Channel
- Advantages and Disadvantages of Mesh Topology
- Cloud Networking - Managing and Optimizing Cloud-Based Networks
- Collision Domain and Broadcast Domain
- Count to Infinity Problem in Distance Vector Routing
- Difference Between Go-Back-N and Selective Repeat Protocol
- Difference between Stop and Wait, GoBackN, and Selective Repeat
- Network Function Virtualization (NFV): transforming Network Architecture with Virtualized Functions
- Network-Layer Security | IPSec Modes
- Next - Prev Network-Layer Security | IPSec Protocols and Services
- Ping vs Traceroute
- Software Defined Networking (SDN): Benefits and Challenges of Network Virtualization
- Software Defined Networking (SDN) vs. Network Function Virtualization (NFV)
- Virtual Circuits vs Datagram Networks
- BlueSmack Attack in Wireless Networks
- Bluesnarfing Attack in Wireless Networks
- Direct Sequence Spread Spectrum
- Warchalking in Wireless Networks
- WEP (Wired Equivalent Privacy)
- Wireless security encryption
- Wireless Security in an Enterprise
- Quantum Networking
- Network Automation
- Difference between MSS and MTU
- What is MTU
- Mesh Networks: A decentralized and Self-Organizing Approach to Networking
- What is Autonomous System
- What is MSS
- Cyber security & Software security
- Information security & Network security.
- Security Engineer & Security Architect
- Protection Methods for Network Security
- Trusted Systems in Network Security
- What are Authentication Tokens in Network security
- Cookies in Network Security
- Intruders in Network Security
- Network Security Toolkit (NST) in virtual box
- Pivoting-Moving Inside a Network
- Security Environment in Computer Networks
- Voice Biometric technique in Network Security
- Advantages and Disadvantages of Conventional Testing
- Difference between Kerberos and LDAP
- Cyber security and Information Security
- GraphQL Attacks and Security
- Application Layer in OSI Model
- Applications of Remote Sensing
- Seven Layers of IT Security
- What is Ad Hoc TCP
- What is Server Name Indication(SNI)
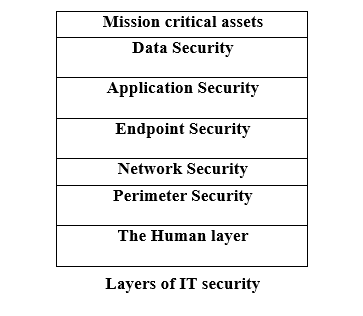
Seven Layers of IT Security
This article will help you in providing a good understanding of the seven layers of IT security. Before moving on to the main topic first let us know what are IT security layers.
What are IT security Layers?
IT security layers refer to the several levels of security controls that may be used to defend against online attacks. As we know, there are many other alternatives, but the "defence in depth" paradigm is a typical framework for layering cybersecurity measures. To provide a more thorough and effective defence against cyber-attacks, this concept entails putting in place many layers of security measures.
Layers of IT security
There are seven layers of IT security that are mentioned and explained below:
Layer1- Mission critical assets
Layer2- Data security
Layer3- Application Security
Layer4- Endpoint Security
Layer5- Network Security
Layer6- Perimeter Security
Layer7- The Human layer
Let us understand each layer from the bottom to the top manner.
Layer 7 - The Human Layer
Humans alone are responsible for 90% of data breaches, making them the weakest link in any cyber security strategy. Human security includes the following measures:
- Phishing simulations,
- Access management guidelines which controls the mission-critical assets from a range of human threats,
- Cybercriminals,
- Malicious insiders, and
- Irresponsible users.
Security Plan: The greatest approaches to keep the human layer safe comes under the education and training. This includes guidelines on how to spot and respond to phishing attempts, strong password techniques, system hardening, and cyber security awareness.
Access restriction is a good idea for safeguarding the human layer since they can lessen the potential damage from a successful assault.
Layer 6 - Perimeter Security
The perimeter security controls have digital and physical security measures that protect the entire business. When identifying the type of data being transferred across this layer, we must first determine our perimeter. After that, we must secure both data and the device.
Security Plan: Installation of firewalls, data encryption, antivirus software, and device management are the security strategies which are crucial when a company allows their employees to use their own device. This layer also establish a safe demilitarised zone to enhance security.
Layer5 - Network Security
There are various methods of network security used to protect a company's network and helps in preventing unauthorized access. The main concern with the network layer is what people and devices may access once they are on a network. Network Security methods/techniques are mainly used to protect the important data of an organization from network attacks.
Security Plan: If no individual has access to everything, then any successful hack only compromises a tiny piece of the network. At this stage, the security measures only allow the devices and workers to access only those network resources that are essential for them to perform their tasks.
Layer4 - Endpoint Security
Any device that is linked to your network is referred to as an endpoint. As we mentioned above, there are so many endpoints on networks nowadays that it may be a bit daunting. To manage and monitor these devices, it is crucial to present the robust policy.
Security Plan: At this level, encryption is essential, but it can't merely apply to your data. To make sure that the devices themselves are operating in safe settings, endpoint encryption must be installed.
A crucial component of endpoint security is mobile device management (MDM). MDM is a system which give permissions to access the devices remotely, with this it also lets you to restrict access to some networked devices, which is excellent feature. You may use this capability to lock down mobile devices and erase all of their data to prevent from future damage.
Layer3 - Application Security
This layer of IT security covers all the programs and applications which are using by the user. Various programs like Microsoft Office, Teams, Zoom, and others, which performs our daily tasks would be secured.
Security Plan: In this situation, the simplest thing you can do to update your programs or applications regularly. Due to this, it is possible to secure and safe the application and also helps in ensuring that the existing security flaws are fixed.
In this stage, the security measures will use sandboxes for browser-based applications and the software restriction guidelines to prevent the unauthorised software which is being executed on your network. Along with this, we can safe the things by using the next-generation firewalls which are working with the integrated app protection.
Layer2 - Data Security
Cybercriminals mainly target the data in almost every instance. This layer mainly deals with providing high security to the data. As, the data is considered as heart and soul for a business.
Your company's specific needs will determine the type of data you have, but it may include customer information, payment information, social security numbers, trade secrets (and other intellectual property), and healthcare data.
Security Plan: At this stage, file and disc encryption, regular backups of all crucial data and operations, two-factor authentication, enterprise rights management, and policies are ensuring that data is deleted from inactive devices or that are being given to another person for use.
Layer1 - Mission Critical Assets
Anything without which your company cannot thrive is listed here. This covers operating systems, cloud infrastructure, software tools, and electronic health records. The difficulty at this layer is that what is crucial for one business may not be crucial for yours. To secure your business, you must first identify the essential elements of it.
Security Plan: In this level, you have to decide the important apsects to your business.


