Tutorial
Physical Layer
Data Link layer
Network Layer
Routing Algorithm
Transport Layer
Application Layer
Network Security
Misc
- Router
- OSI vs TCP/IP
- TCP vs UDP
- Transmission Control Protocol
- TCP port
- IPv4 vs IPv6
- ARP Packet Format
- ARP Table
- Working of ARP
- FTP Client
- FTP Commands
- FTP Server
- I2C Protocol
- Sliding Window Protocol
- SPI Protocol
- IP
- ARP Commands
- ARP
- Address Resolution Protocol
- ARP and its types
- TCP Retransmission
- CAN protocol
- HTTP Status Codes
- HTTP vs HTTPS
- RIP Protocol
- UDP Protocol
- ICMP Protocol
- MQTT protocol
- OSPF Protocol
- Stop and Wait Protocol
- IMAP Protocol
- POP Protocol
- CIFS
- DAS
- DIMM
- iSCSI
- NAS (Network Attached Storage)
- NFS
- NVMe
- SAN
- Border Gateway Protocol
- Go-Back-N ARQ
- RJ Cable
- Difference between Connection-Oriented and Connectionless Service
- CDMA vs. GSM
- What is MAC Address
- Modem vs. Router
- Switch Vs. Router
- USB 2.0 vs 3.0
- Difference between CSMA CA and CSMA CD
- Multiple access protocol- ALOHA, CSMA, CSMA/CA and CSMA/CD
- URI vs URL
- IMAP vs. POP3
- SSH Meaning| SSH Protocol
- UTP vs STP
- Status Code 400
- MIME Protocol
- IP address
- proxy server
- How to set up and use a proxy server
- network security
- WWW is based on which model
- Proxy Server List
- Fundamentals of Computer Networking
- IP Address Format and Table
- Bus topology and Ring topology
- Bus topology and Star topology
- Circuit Switching and Packet switching?
- Difference between star and ring topology
- Difference between Router and Bridge
- TCP Connection Termination
- Image Steganography
- Network Neutrality
- Onion Routing
- Adaptive security appliance (ASA) features
- Relabel-to-front Algorithm
- Types of Server Virtualization in Computer Network
- Access Lists (ACL)
- What is a proxy server and how does it work
- Digital Subscriber Line (DSL)
- Operating system based Virtualization
- Context based Access Control (CBAC)
- Cristian's Algorithm
- Service Set Identifier (SSID)
- Voice over Internet Protocol (VoIP)
- Challenge Response Authentication Mechanism (CRAM)
- Extended Access List
- Li-fi vs. Wi-fi
- Reflexive Access List
- Synchronous Optical Network (SONET)
- Wifi protected access (WPA)
- Wifi Protected Setup (WPS)
- Standard Access List
- Time Access List
- What is 3D Internet
- 4G Mobile Communication Technology
- Types of Wireless Transmission Media
- Best Computer Networking Courses
- Data Representation
- Network Criteria
- Classful vs Classless addressing
- Difference between BOOTP and RARP in Computer Networking
- What is AGP (Accelerated Graphics Port)
- Advantages and Disadvantages of Satellite Communication
- External IP Address
- Asynchronous Transfer Mode (ATM)
- Types of Authentication Protocols
- What is a CISCO Packet Tracer
- BOOTP work
- Subnetting in Computer Networks
- Mesh Topology Advantages and Disadvantages
- Ring Topology Advantages and Disadvantages
- Star Topology Advantages and Disadvantages
- Tree Topology Advantages and Disadvantages
- Zigbee Technology-The smart home protocol
- Network Layer in OSI Model
- Physical Layer in OSI Model
- Data Link Layer in OSI Model
- Internet explorer shortcut keys
- Network Layer Security | SSL Protocols
- Presentation Layer in OSI Model
- Session Layer in OSI Model
- SUBNET MASK
- Transport Layer Security | Secure Socket Layer (SSL) and SSL Architecture
- Functions, Advantages and Disadvantages of Network Layer
- Protocols in Noiseless and Noisy Channel
- Advantages and Disadvantages of Mesh Topology
- Cloud Networking - Managing and Optimizing Cloud-Based Networks
- Collision Domain and Broadcast Domain
- Count to Infinity Problem in Distance Vector Routing
- Difference Between Go-Back-N and Selective Repeat Protocol
- Difference between Stop and Wait, GoBackN, and Selective Repeat
- Network Function Virtualization (NFV): transforming Network Architecture with Virtualized Functions
- Network-Layer Security | IPSec Modes
- Next - Prev Network-Layer Security | IPSec Protocols and Services
- Ping vs Traceroute
- Software Defined Networking (SDN): Benefits and Challenges of Network Virtualization
- Software Defined Networking (SDN) vs. Network Function Virtualization (NFV)
- Virtual Circuits vs Datagram Networks
- BlueSmack Attack in Wireless Networks
- Bluesnarfing Attack in Wireless Networks
- Direct Sequence Spread Spectrum
- Warchalking in Wireless Networks
- WEP (Wired Equivalent Privacy)
- Wireless security encryption
- Wireless Security in an Enterprise
- Quantum Networking
- Network Automation
- Difference between MSS and MTU
- What is MTU
- Mesh Networks: A decentralized and Self-Organizing Approach to Networking
- What is Autonomous System
- What is MSS
- Cyber security & Software security
- Information security & Network security.
- Security Engineer & Security Architect
- Protection Methods for Network Security
- Trusted Systems in Network Security
- What are Authentication Tokens in Network security
- Cookies in Network Security
- Intruders in Network Security
- Network Security Toolkit (NST) in virtual box
- Pivoting-Moving Inside a Network
- Security Environment in Computer Networks
- Voice Biometric technique in Network Security
- Advantages and Disadvantages of Conventional Testing
- Difference between Kerberos and LDAP
- Cyber security and Information Security
- GraphQL Attacks and Security
- Application Layer in OSI Model
- Applications of Remote Sensing
- Seven Layers of IT Security
- What is Ad Hoc TCP
- What is Server Name Indication(SNI)
4G Mobile Communication Technology
Mobile communication is a way to communicate with other people at a different locations without any physical connection. It enables to transmission of voice and multimedia data from one mobile or computer device to another without any need for a physical connection between them. A Mobile phone or Cellular phone is an example of mobile communication.
Since the introduction of mobile communication, this technology has come a long way and has evolved a lot. Many technological developments have been made to make mobile communication more efficient and serve users better. It was introduced as 1G (First Generation- Voice-only communication), and today we are widely using 4G technology. 4G is the fourth Generation of mobile network technology, which is the successor of 3G and preceded by the 5G network. It provides a much higher data transmission speed than its successor networks, making it preferable at this stage of a fast lifestyle. In this topic, we will learn more about 4G Mobile communication, its introduction, working, availability, etc.
What is 4G?
4G is known as the fourth Generation of Mobile Communication or wireless communication technology, which is the successor of the 3G network. It provides high data transmission speed and is suitable for HD video calling, fast download and upload, live streaming, online gaming, etc. A 4G system must adhere to the capabilities and features specified by the ITU(International Telecommunication Union) in IMT advanced, including transmission technology and data speed. 4G network provides up to 100 Mbps speed to users, far higher than a 3G network.
4G enables users to stream high-definition audio and videos without interruption due to its high speed. It also facilitates wireless broadband that allows the users to access the internet without any need for fixed wired.
Features of 4G Mobile Network
- It aims to provide high data transmission speed without interruption at any location.
- As per ITU standard, a 4G network system must have the highest data rates of 100Mbs for highly mobile stations like trains, cars etc.
- It provides seamless switching across heterogenous network areas.
- It is very well suitable for the transmission of voice, data, signals, multimedia, wireless internet, and other broadband services.
- It provides high speed at a low cost.
- Global mobility, service portability, scalable mobile networks.
- It provides a better way for scheduling and calling admission control techniques.
Categories of 4G
A 4G network is categorized into two categories:
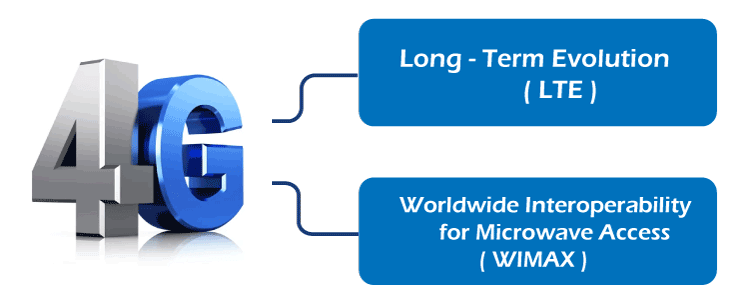
- LTE (Long-Term Evolution)
LTE stands for Long-Term evolution, a standard for high-speed wireless communication commonly used in 4G connections. It is technically different from 4G, i.e., 4G and 4G LTE are not technically the same. LTE data is transmitted with faster speed and lower latency. The connectivity for the LTE network is available universally around the world for both customers and industrial applications.
The term LTE is specifically used for marketing purposes, as specified speed and technical specifications defined for 4G were not achievable when it was introduced. Hence LTE provides much more speed and bandwidth than 3G but does not imply a specific rate. Depending on the carrier, speed ranges from 20 Mbps to 100 Mbps - Worldwide Interoperability for Microwaves Access (WiMAX)
WiMAX is a type or representative of 4G wireless internet. It is similar to wifi, which enables the user to access the internet without the need for wires. However, it is a bit different from wifi, as unlike wifi (which covers a building or city), it can cover vast distances such as cell phone networks with high-speed internet access similar to broadband. A Mobile WiMax is a type of 4G network, but all 4G networks are not WiMAX. The peak data rates offered by WiMAX are 128 Mbps for downlink and 56 Mbps for uplink over 20 MHz wide channels.
How does 4G Network work?
At a basic level, a 4G mobile connection transmits the signal via an antenna over radio frequencies, which allows mobile devices to connect to mobile networks.
The 4G capabilities for transmitting and receiving the signal are based on Multiple Input and Multiple Output (MIMO) and Orthogonal Frequency Division Multiplexing (OFDM) technologies. Due to these technologies, 4G offers high capacity and bandwidth comparison to 3G.
MIMO technology reduces network congestion as compared to 3G, and hence services can be served to more users without network congestion.
4G network supports all-IP standards for both voice and data transmission. 4G is more efficient for mobile network providers to operate and optimize than managing different network technologies for voice and data because of the all-IP network.
Advantages of 4G
- With a 4G connection, users don't need any phone line or wired connection. Instead, it works using the same internet connection as the mobile phone.
- 4G provides portability, which means with this connection, users can take the internet anywhere at any time.
- With 4G, the cost of internet services has fallen down highly compared to 3G. Hence, it gives high-speed internet at less cost.
- Nowadays, everything is being hosted online, and hence users require high internet to work with cloud services, and it is possible with 4G (and upcoming 5G) connections.
Disadvantages of 4G
- It depends on the network signal; if the signal gets weaker, then the user experiences slow and unstable services.
- It needs more battery consumption.
Future of 4G
Although 4G is much more efficient and fast compared to 3G, it is still lacking compatibility with the fast-growing technologies that need many high-speed networks. Hence after 4G, 5G Technology is ready to make a boom in the mobile communication sector. 5G mobile phones with extremely high data rates, IP core, and worldwide coverage will offer features which have not been imagined so far.
Currently, 5G is neither available worldwide nor being used universally as it requires a lot of changes in network infrastructure and other things. It will drastically change the current landscape of mobile communication. It is currently available in the US, China, Canada, Italy etc. However, very soon, it will be available worldwide.


